
Seven types of unauthorised access and how to prevent them occurring
From being polite by holding doors open for an assumed colleague, to forging access credentials, there are various types of unauthorised access that can put a building or organisation at risk. The short video below briefly outlines the seven types, but for more detail continue reading…
When deciding what type of entrance control system to install, it is important to evaluate what you need it to do, including which data you would like to capture and how it should be integrated with building management systems. Most importantly, you should consider which types of behaviour to encourage and discourage – particularly unauthorised access.
Here we round up the different types of unauthorised access that can leave buildings and organisations at risk, and how best to address them to ensure the highest level of security for your people and assets.
Tailgating
Tailgating, also known as piggybacking, is the act of following someone through an open door unauthorised. Even if there is no intent to cause disruption, the follower is the one at fault and the person being followed may not even be aware of the act.
Recognised as a common type of security breach and, whilst often innocent, tailgating can expose your employees and assets to unknown risks from people outside of the organisation, who may wish to cause harm.

While training for authorised users on awareness and security protocol is helpful, installing entrance control turnstiles is a more effective method of enforcing entry to one authorised individual at a time.
For example, the Fastlane Speedgate and Fastlane Plus ranges use advanced infrared technology to optimise and monitor the passage of individuals entering and leaving a facility, and fast-acting glass barriers or barrier arms to physically deter unauthorised access and detect tailgating as close as 5mm, only allowing one user to enter per valid credential presented.
Collusion
Whilst tailgating is a known security threat, an organisation shouldn’t dismiss the threat that arises through collusion by staff with authorised access, whether this be intentional or just an employee ‘being kind’ and letting someone through an access-controlled door.
 Unlike tailgating, collusion is when individuals purposefully act to let someone who otherwise wouldn’t gain access, in through a secured point. With collusion, the one with the keycard is at fault as the intention is to bypass the security measures in place in order for someone unauthorised to gain access. Again, the reasons for acting in such a way may be innocent – and it could be as simple as someone forgetting their own keycard and temporarily borrowing a colleague’s – but equally, a system that allows for this could leave you vulnerable.
Unlike tailgating, collusion is when individuals purposefully act to let someone who otherwise wouldn’t gain access, in through a secured point. With collusion, the one with the keycard is at fault as the intention is to bypass the security measures in place in order for someone unauthorised to gain access. Again, the reasons for acting in such a way may be innocent – and it could be as simple as someone forgetting their own keycard and temporarily borrowing a colleague’s – but equally, a system that allows for this could leave you vulnerable.
Dual Entry Collusion
This refers to the act of two people attempting unauthorised dual entry using collusion through an entrance control system, and it has only recently become relevant due to the advent of wider turnstile lanes.
In response to changing regulations and to meet customer demands for wider lanes for both pedestrian and wheelchair users’ comfort, we developed extensions to our range of Fastlane Speedgates, launching the Glassgate 155 at the end of 2017 and, most recently, the Glassgate 400 Plus. Both models enable Fastlane customers to install turnstile lanes of up to 1200mm wide, significantly wider than the standard 660mm and 914mm DDA and ADA compliant lanes that have previously been supplied.
But, with the development of wider lanes came the potential for dual entry collusion. Driven by this emerging security risk, we developed new optical technology to prevent this form of breach.
The new optical technology is part of IDL’s policy of continuous improvement to our products and services, including wider redevelopment of our optical system which is purpose designed and built by our in-house engineers for exclusive use in Fastlane turnstiles.
Pushing, Crawling Under or Climbing Over
This type of unauthorised access involves individuals pushing barriers, climbing over or crawling underneath them to gain access to a building.
With Fastlane technology, our turnstiles detect pushed barriers, alerting security staff to unauthorised entry attempts by triggering audible alarms.

In addition to the barriers themselves, Fastlane also features multiple beam paths which include an anti-crawl system, creating an alert should a person try and enter under the barrier arms. In the event of a pedestrian attempting to enter without permission, Fastlane products feature a secure two-stage alarm response, sounding an alarm and activating the barriers to deter the unauthorised individual. If the entrant continues to attempt to push past the barrier arms then a second alarm sounds, optionally triggering other security actions such as CCTV or locking internal doors by integration with compatible systems. Recently introduced to the range are the Fastlane climb sensors too, which detect attempts to bypass the barriers by climbing over.
Passbacks
This occurs when an authorised user passes through a doorway using an authorisation card, and then passes an unauthorised individual their card to get through as well. This results in an unidentified individual being unaccounted for in a facility, thereby constituting a security risk.
Our Door Detective range solves the problem of passbacks by monitoring the throughput of open, access-controlled doorways, corridors and passageways. Using multiple infrared beams from enclosures mounted near the door frames, Door Detective accurately monitors movement in both directions each time a person presents electronic credentials to pass through the doorway, thereby eliminating unauthorised visits and preventing the credential from letting a second person through the door. It thereby raises the security level of any door it is used on, and protects the area from unauthorised entry through the door after an authorised person has used it and passed through.
This additional level of security adds sensitivity and also signals activity such as unauthorised entrants, tailgating, collusion and obstruction, ideal for protecting internal doors in data centres, executive floors, laboratories and office environments.
Fraudulent use of access cards
Access cards can pose similar problems to the use of keys, including the potential to be lost, stolen or shared. While access cards can identify users who swipe in at an access control reader, they can be duplicated, are susceptible to wear and tear and unless paired with another means of identifying whether the user is who the card was originally intended for, could leave you susceptible to fraudulent use.
 Introducing photo identification cards makes this security method more reliable, as does utilising biometric technology such as fingerprinting, voice and facial recognition. Biometric security measures mean that the individual accessing secure areas or information is not just an individual holding the proper access card credentials, but is in fact the person who has been granted access. It is also hard to fake, given that the personal information collected is unique.
Introducing photo identification cards makes this security method more reliable, as does utilising biometric technology such as fingerprinting, voice and facial recognition. Biometric security measures mean that the individual accessing secure areas or information is not just an individual holding the proper access card credentials, but is in fact the person who has been granted access. It is also hard to fake, given that the personal information collected is unique.
Fastlane turnstiles and our Door Detective range is capable of integrating with ‘deep learning’ artificial intelligence facial recognition systems to provide intelligent entrance control, eradicating the fraudulent use of access credentials. We have covered this topic previously, here.
Door propping
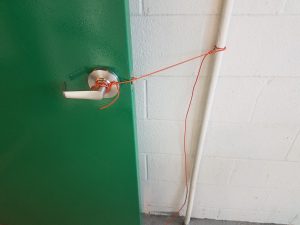 The propping open of doors for convenience is similar to collusion, and a common way unauthorised individuals attempt to gain access to a building. An emergency exit held open by a fire extinguisher is not an uncommon sight! This clearly is an invitation for someone unauthorised to enter the building, and so it is important that the security team can be quickly and easily made aware of this.
The propping open of doors for convenience is similar to collusion, and a common way unauthorised individuals attempt to gain access to a building. An emergency exit held open by a fire extinguisher is not an uncommon sight! This clearly is an invitation for someone unauthorised to enter the building, and so it is important that the security team can be quickly and easily made aware of this.
Fastlane Door Detective has the capability to detect when doors are propped open, and in which direction individuals are passing through an access-controlled doorway, thus alerting security personnel with alarms when this occurs.
For more information about controlling and monitoring the various kinds of unauthorised access using the Fastlane range of turnstiles or Door Detective products, get in touch with our team today on +44 (0)208 890 5550 or email info@fastlane-turnstiles.com.
In other news:



